Ecosyste.ms: Advisories
An open API service providing security vulnerability metadata for many open source software ecosystems.
Security Advisories: GSA_kwCzR0hTQS12NHYyLThoODgtNjVxas4AA3W6
Attribute Injection leading to XSS(Cross-Site-Scripting)
Summary
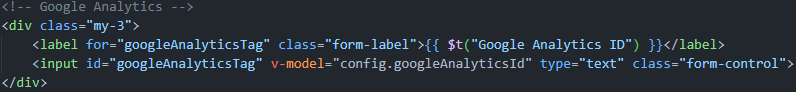
Google Analytics element Attribute Injection leading to XSS
Details
Since the custom status interface can set an independent Google Analytics ID and the template has not been sanitized, there is an attribute injection vulnerability here, which can lead to XSS attacks.
PoC
- Run the latest version of the louislam/uptime-kuma container and initialize the account password.
- Create a new status page.
- Edit the status page and change the Google Analytics ID to following payload(it only works for firefox. Any attribute can be injected, but this seems the most intuitive):
123123" onafterscriptexecute=alert(window.name+1),eval(window.name) a="x
- Click Save and return to the interface. XSS occurs.
screenshots:


JSON: https://advisories.ecosyste.ms/api/v1/advisories/GSA_kwCzR0hTQS12NHYyLThoODgtNjVxas4AA3W6
Source: GitHub Advisory Database
Origin: Unspecified
Severity: Moderate
Classification: General
Published: about 1 year ago
Updated: about 1 year ago
CVSS Score: 6.1
CVSS vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N
EPSS Percentage: 0.00075
EPSS Percentile: 0.34776
Identifiers: GHSA-v4v2-8h88-65qj, CVE-2023-49276
References:
- https://github.com/louislam/uptime-kuma/security/advisories/GHSA-v4v2-8h88-65qj
- https://nvd.nist.gov/vuln/detail/CVE-2023-49276
- https://github.com/louislam/uptime-kuma/commit/f28dccf4e11f041564293e4f407e69ab9ee2277f
- https://github.com/advisories/GHSA-v4v2-8h88-65qj
Blast Radius: 1.0
Affected Packages
npm:uptime-kuma
Dependent packages: 0Dependent repositories: 0
Downloads: 27 last month
Affected Version Ranges: >= 1.20.0, <= 1.23.6
Fixed in: 1.23.7
All affected versions:
All unaffected versions: